Smartwatch Integration with Smart Home Devices
Address smartwatch security concerns. Learn about potential vulnerabilities and the solutions being developed to protect user data.
Smartwatch Security Vulnerabilities and Solutions
Understanding Smartwatch Security Risks
Smartwatches have become an indispensable part of our daily lives, offering convenience, health monitoring, and connectivity right on our wrists. However, with great convenience comes great responsibility, especially when it comes to data security. These tiny computers are constantly collecting sensitive information, from our heart rate and sleep patterns to our location and even financial transactions. Understanding the potential security risks associated with smartwatches is the first step in protecting your personal data.
One of the primary concerns is the sheer volume and sensitivity of the data smartwatches collect. Think about it: your smartwatch knows where you are, how active you are, who you communicate with, and potentially even your payment details. If this data falls into the wrong hands, it could lead to identity theft, financial fraud, or even physical security risks if your location data is compromised. Moreover, many smartwatches are connected to your smartphone, creating another potential entry point for malicious actors if the smartwatch itself isn't adequately secured.
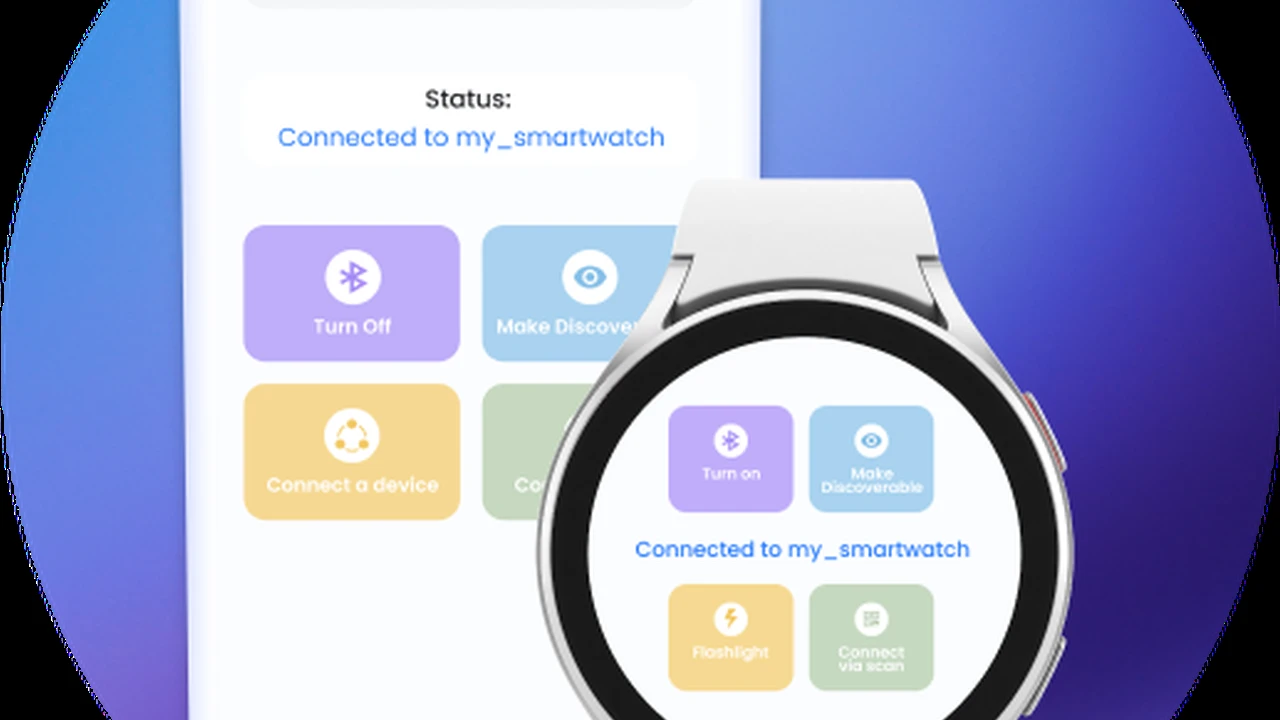
Another significant risk lies in the connectivity features of smartwatches. Bluetooth, Wi-Fi, and cellular (LTE) connections are all potential vectors for attacks. Unsecured Bluetooth connections can be intercepted, allowing unauthorized access to data or even control over the device. Similarly, connecting to unsecure Wi-Fi networks can expose your data to eavesdropping. LTE-enabled smartwatches, while offering greater independence from your phone, also introduce the same cellular network vulnerabilities as smartphones.
Finally, the apps you install on your smartwatch can also pose a risk. Just like smartphone apps, smartwatch apps can have vulnerabilities or be designed with malicious intent. Granting excessive permissions to an app could allow it to access sensitive data it doesn't need, or even to control certain functions of your device without your knowledge.
Common Smartwatch Vulnerabilities Explained
Let's dive deeper into some of the most common vulnerabilities that smartwatches face. Knowing these can help you be more vigilant and take proactive steps to protect yourself.
Bluetooth Eavesdropping and Hijacking
Bluetooth is the most common way smartwatches connect to smartphones. While Bluetooth Low Energy (BLE) has improved security features compared to older versions, vulnerabilities can still exist. Eavesdropping attacks involve an attacker intercepting data transmitted over Bluetooth, potentially gaining access to notifications, messages, or even health data. Hijacking, on the other hand, involves an attacker taking control of the Bluetooth connection, which could allow them to send commands to your smartwatch or even your connected phone.
For example, a researcher might demonstrate how to intercept data from a popular fitness tracker using readily available tools, highlighting the need for strong encryption and authentication protocols in Bluetooth communication. While most modern smartwatches use secure pairing methods, older devices or those with outdated firmware might be more susceptible.
Insecure Wi-Fi Connections and Data Interception
Many smartwatches can connect to Wi-Fi networks, especially for larger data transfers or when out of Bluetooth range of your phone. Connecting to public or unsecured Wi-Fi networks is a major risk. An attacker on the same network can easily intercept unencrypted data, including login credentials, personal messages, or even payment information if you're using your smartwatch for transactions.
Imagine you're at a coffee shop, and your smartwatch automatically connects to their public Wi-Fi. If that network isn't properly secured, anyone else on the network with the right tools could potentially see the data your smartwatch is sending and receiving. This is why it's crucial to only connect to trusted, password-protected Wi-Fi networks.
Malicious Apps and Permission Exploitation
The app ecosystem for smartwatches is growing, but so is the potential for malicious apps. An app might request permissions that seem innocuous but could be exploited. For instance, an app that requests access to your location data for a seemingly legitimate purpose might then sell that data to third parties or use it for nefarious activities.
Some malicious apps might even be designed to steal credentials, install malware on your connected phone, or drain your battery to disrupt your device's functionality. Always be cautious about the apps you download, especially from third-party app stores, and review the permissions they request carefully.
Firmware Vulnerabilities and Outdated Software
Like any other computing device, smartwatches run on firmware, which is essentially their operating system. Software bugs and vulnerabilities can exist in this firmware. If these vulnerabilities are not patched through regular updates, they can be exploited by attackers to gain unauthorized access, inject malicious code, or disrupt the device's operation.
Manufacturers regularly release firmware updates to address security flaws and improve performance. Neglecting to install these updates leaves your smartwatch exposed to known vulnerabilities. It's like leaving your front door unlocked when you know there's a burglar in the neighborhood.
Physical Security Risks and Data Theft
Smartwatches are small and easily lost or stolen. If your smartwatch is not properly secured with a strong passcode or biometric authentication, a thief could potentially access your personal data, notifications, or even use it for contactless payments if your payment cards are linked.
Consider a scenario where your smartwatch is stolen. If it's unlocked, the thief could potentially view your recent messages, access your calendar, or even use features like 'Find My Phone' to locate your smartphone. This highlights the importance of having robust physical security measures in place.
Solutions and Best Practices for Smartwatch Security
Now that we've identified the vulnerabilities, let's talk about what you can do to protect your smartwatch and your data. Implementing these solutions and best practices can significantly reduce your risk.
Enable Strong Passcodes and Biometric Authentication
This is perhaps the most fundamental security measure. Always set a strong passcode on your smartwatch. Many smartwatches also offer biometric authentication, such as PINs or pattern locks that activate when the watch is removed from your wrist. Utilize these features. For example, Apple Watch uses a passcode that locks the device when it detects it's no longer on your wrist. Samsung Galaxy Watch models also offer PIN protection.
Product Examples:
- Apple Watch Series 9: Offers robust passcode protection and wrist detection, automatically locking when removed.
- Samsung Galaxy Watch 6: Features PIN/pattern lock and can be set to lock when taken off the wrist.
- Google Pixel Watch 2: Supports screen lock with a PIN for enhanced security.
Keep Software and Firmware Updated
Regularly check for and install software and firmware updates from your smartwatch manufacturer. These updates often include critical security patches that address newly discovered vulnerabilities. Enabling automatic updates is usually the best approach.
Usage Scenario: Your smartwatch manufacturer releases an urgent security patch for a Bluetooth vulnerability. If you have automatic updates enabled, your watch will download and install it, protecting you from potential exploits. If not, you remain vulnerable until you manually update.
Be Mindful of App Permissions
Before installing any app on your smartwatch, review the permissions it requests. Ask yourself if the app truly needs access to your location, contacts, or health data to function. If an app requests excessive permissions, it's a red flag. Only download apps from official app stores (e.g., Apple App Store, Google Play Store) as they have stricter vetting processes.
Comparison: While both Apple and Google have app review processes, some third-party app stores might be less stringent. Sticking to official sources minimizes the risk of downloading malicious apps.
Use Secure Wi-Fi Networks
Avoid connecting your smartwatch to public or unsecured Wi-Fi networks. If you must use a public network, ensure that any sensitive data transmission is encrypted (e.g., through a VPN on your connected phone, if the smartwatch mirrors its connection). Prioritize connecting to your home or office Wi-Fi, which should be secured with a strong password.
Disable Unnecessary Connectivity Features
If you're not using Wi-Fi or cellular connectivity on your smartwatch, consider disabling them. This reduces the attack surface. For instance, if your smartwatch is primarily used for fitness tracking and is always connected to your phone via Bluetooth, you might not need Wi-Fi enabled all the time.
Enable Find My Device Features
Most modern smartwatches offer 'Find My Device' features (e.g., Apple's Find My, Samsung's SmartThings Find). Enable these features so you can remotely locate, lock, or even wipe your smartwatch if it's lost or stolen. This is crucial for preventing unauthorized access to your data.
Product Examples:
- Apple Watch: Integrates seamlessly with Apple's 'Find My' network, allowing you to locate it on a map, play a sound, or erase its data.
- Samsung Galaxy Watch: Uses SmartThings Find to help locate lost devices, with options to lock or wipe data.
Be Cautious with Notifications
Smartwatches display notifications from your phone, which can include sensitive information like messages, emails, or banking alerts. Configure your notification settings to prevent sensitive content from being displayed on the lock screen or when the watch is unlocked by others. For example, you can set notifications to only show content when you tap on them.
Regularly Review Connected Devices and Accounts
Periodically check the list of devices connected to your smartphone via Bluetooth and remove any unfamiliar or unused connections. Similarly, review the accounts linked to your smartwatch apps and revoke access for any services you no longer use.
Consider Data Encryption
Many modern smartwatches encrypt data stored on the device and data transmitted between the watch and your phone. Ensure this feature is enabled if available. This adds an extra layer of protection in case your device is compromised.
Use Strong, Unique Passwords for Linked Accounts
Your smartwatch often links to various online accounts (e.g., fitness apps, payment services). Ensure that these accounts are protected with strong, unique passwords and, wherever possible, enable two-factor authentication (2FA). If one of these linked accounts is compromised, it could potentially affect your smartwatch's security.
Specific Product Security Features and Pricing Considerations
Let's look at how some popular smartwatches address security and how their features might influence their price.
Apple Watch Series 9
Security Features: Apple Watch is renowned for its robust security. It features on-device encryption for all data, strong passcode protection with wrist detection (locks when removed), and seamless integration with Apple's 'Find My' network for remote location and wiping. Health data is encrypted and protected by your iPhone's passcode. Apple's App Store has a rigorous review process, minimizing malicious apps.
Usage Scenario: If you lose your Apple Watch, you can use the 'Find My' app on your iPhone or iCloud.com to locate it, play a sound, mark it as lost (which locks it and displays a custom message), or remotely erase all its data. This provides significant peace of mind.
Pricing: Starts around $399 for the GPS model, with cellular models and larger sizes costing more. The premium price reflects its advanced features, strong ecosystem integration, and robust security.
Samsung Galaxy Watch 6
Security Features: Samsung Galaxy Watches run on Wear OS (co-developed with Google) and incorporate Samsung Knox security platform. Knox provides multi-layered security from the hardware up, protecting data and ensuring the integrity of the device. It offers PIN/pattern lock, wrist detection, and integration with SmartThings Find for remote management. Data is encrypted on the device.
Usage Scenario: Samsung Knox helps protect your payment information when using Samsung Pay on your watch. Even if your watch is compromised, the secure environment provided by Knox makes it difficult for attackers to access sensitive financial data.
Pricing: Starts around $299 for the Bluetooth model, with LTE versions and Classic models being more expensive. The price reflects its advanced features, Wear OS capabilities, and Samsung's commitment to security through Knox.
Google Pixel Watch 2
Security Features: As a Google device, the Pixel Watch 2 benefits from Google's security infrastructure. It runs Wear OS and includes features like a screen lock with a PIN. Data is encrypted, and it integrates with Google's 'Find My Device' service. Google Play Store's app vetting process also contributes to app security.
Usage Scenario: If you misplace your Pixel Watch 2, you can use the 'Find My Device' app on your Android phone or via a web browser to locate it, make it ring, or remotely erase its data, similar to how you'd manage a lost Android phone.
Pricing: Starts around $349 for the Wi-Fi model, with LTE versions costing more. Its price point is competitive, offering a pure Wear OS experience with Google's security backing.
Garmin Forerunner Series (e.g., Forerunner 965)
Security Features: Garmin smartwatches, while primarily focused on fitness, also incorporate security measures. They typically use PIN locks for Garmin Pay (their contactless payment system) and offer data encryption. While not as deeply integrated with a smartphone ecosystem for general security as Apple or Samsung, their focus on on-device data protection for fitness metrics is strong.
Usage Scenario: When using Garmin Pay, you'll be prompted for a PIN on your watch, adding a layer of security to your transactions even if your watch is unlocked for general use. This is particularly useful for athletes who might not want to carry their phone or wallet during workouts.
Pricing: Varies widely depending on the model, with the Forerunner 965 around $599. The price reflects its advanced sports tracking capabilities, long battery life, and durable build, with security features tailored to its use case.
The Evolving Landscape of Smartwatch Security
The security landscape for smartwatches is constantly evolving. As these devices become more sophisticated and integrate more deeply into our lives, so too do the methods employed by malicious actors. Manufacturers are continuously working to improve security through hardware-level protections, secure software development practices, and regular updates.
The increasing adoption of secure elements for payment processing, similar to those found in smartphones, is a positive trend. These dedicated chips provide a highly secure environment for storing sensitive data like credit card information, making it extremely difficult for attackers to access. Furthermore, advancements in biometric authentication, such as more reliable heart rate or even vein pattern recognition, could offer even more secure ways to unlock and authenticate on smartwatches in the future.
The industry is also moving towards more robust privacy controls, giving users greater transparency and control over their data. This includes clearer explanations of what data is collected, how it's used, and easier ways to manage app permissions. As smartwatches become more integral to healthcare and personal finance, these privacy considerations will become even more critical.
Ultimately, while manufacturers play a crucial role in building secure devices, user vigilance remains paramount. By staying informed about potential risks and consistently applying best practices, you can significantly enhance the security of your smartwatch and protect your valuable personal data.
:max_bytes(150000):strip_icc()/277019-baked-pork-chops-with-cream-of-mushroom-soup-DDMFS-beauty-4x3-BG-7505-5762b731cf30447d9cbbbbbf387beafa.jpg)





